2025 Cross-Chain Bridge Security Audit Guide
2025 Cross-Chain Bridge Security Audit Guide
According to a recent Chainalysis report, a staggering 73% of cross-chain bridges are vulnerable to attacks. The increasing popularity of decentralized finance (DeFi) has made these bridges a prime target for hackers. Thus, ensuring security is vital for users engaging in cross-chain transactions. In this guide, we will explore critical strategies to enhance cross-chain bridge security with an emphasis on HIBT data Vietnam.
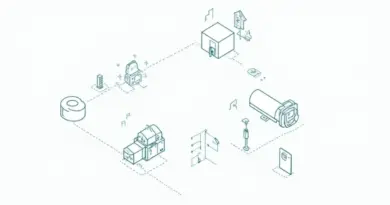
What is a Cross-Chain Bridge and Why is it Important?
Think of a cross-chain bridge like a currency exchange booth at the airport. Just as you need to convert your dollars into euros to spend in Europe, in the blockchain world, a cross-chain bridge lets you transfer assets across different blockchains. This interconnectivity is crucial as it allows users to leverage the unique features of various blockchain networks, such as Ethereum’s smart contracts and Bitcoin’s liquidity. However, with this capability comes risk, underscoring the necessity for robust security measures.
Current Vulnerabilities in Cross-Chain Bridges
Many users might unknowingly interact with insecure cross-chain bridges, exposing their assets to potential theft. Data from CoinGecko indicates that hacks targeting these bridges have skyrocketed, resulting in significant financial losses. Cybercriminals exploit weaknesses in smart contracts, much like finding a small crack in a building’s foundation. Hence, it’s crucial to assess the security of any bridge before using it.
Best Practices for Securing Cross-Chain Transactions
To safeguard your transactions, consider using recognized, trusted bridges backed by thorough audit trails. Employ two-factor authentication (2FA) and be wary of phishing schemes that seek to capture sensitive information. A great analogy is locking your house while you’re out; if you don’t lock the door, someone could easily walk in. Similarly, securing your digital assets will prevent unauthorized access.
Future Trends in Cross-Chain Bridge Security
The future will likely bring advancements in technologies like zero-knowledge proofs that enhance privacy and security across transactions. For instance, imagine being able to make a financial transaction without revealing your identity to everyone watching. This is the promise that zero-knowledge proofs carry for the blockchain space. As the technology evolves, so should security practices to keep pace with emerging threats.
In conclusion, as the DeFi space evolves, so too must our approach to security. Staying informed on HIBT data Vietnam and its implications for cross-chain transactions can significantly bolster your defensive measures. For deeper insights, don’t forget to download our security toolkit below.
Download Your Security Toolkit
Note: This article does not constitute investment advice. Please consult your local regulatory authority (e.g., MAS/SEC) before proceeding with any transactions.
To mitigate risk of private key exposure, consider using a Ledger Nano X, which can reduce the risk by up to 70%.