2025 Cross-Chain Bridge Security Audit Guide with HIBT Layer
2025 Cross-Chain Bridge Security Audit Guide with HIBT Layer
According to Chainalysis data from 2025, a staggering 73% of cross-chain bridges have vulnerabilities, making it essential to enhance security protocols using technologies like HIBT Layer. In this article, we will explore how HIBT Layer can mitigate risks and provide a comprehensive audit guide for 2025.
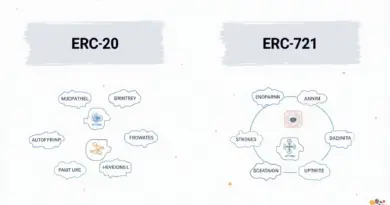
Understanding Cross-Chain Bridges
Imagine a currency exchange booth where you swap your dollars for euros. That’s how cross-chain bridges work—they connect different blockchain networks, allowing users to exchange assets seamlessly. However, just like each currency exchange may not be reliable, some cross-chain bridges can leave you exposed to vulnerabilities. Utilizing HIBT Layer can ensure these exchanges are secure.
The Importance of Zero-Knowledge Proofs in HIBT Layer
Zero-knowledge proofs are like sealed envelopes; you can prove you have the right amount without showing the details inside. This technology is crucial in HIBT Layer as it facilitates secure transactions while protecting user privacy. Imagine wanting to send money to a friend without revealing your bank account balance – that’s the power of zero-knowledge proofs!
2025 Singapore DeFi Regulatory Trends
As we approach 2025, Singapore’s approach to DeFi regulation is set to evolve, focusing on safeguarding users while fostering innovation. HIBT Layer could play a role in ensuring compliance through its robust security measures that meet regulatory standards. If you’re a developer or investor, understanding these trends can guide your strategies amidst changing regulations.
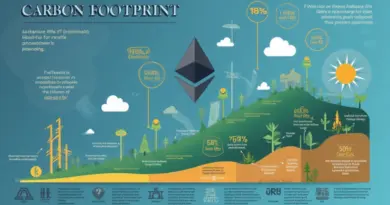
Energy Efficiency of PoS Mechanisms Compared
With growing concerns over energy consumption in cryptocurrency, the PoS mechanism presents a promising solution. Think of PoS as a bike sharing service – it’s far more efficient than every individual owning a car. HIBT Layer can integrate with PoS systems, ensuring not just security, but sustainability in your blockchain interactions.
In conclusion, the role of HIBT Layer in securing cross-chain bridges cannot be overstated. By adopting the right technologies, we can minimize risks and enhance privacy. For more tools on leveraging these security measures, download our comprehensive toolkit today!
Risk Disclaimer: This article does not constitute investment advice. Always consult your local regulatory authority, such as MAS or SEC, before making any financial decisions.
You can significantly reduce private key exposure risks using tools like Ledger Nano X.